Create a Bot for the Telegram Alert
- Open Telegram messenger, sign in to your account or create a new one
- Enter @Botfather in the search tab and choose this bot. (Official Telegram bots have a blue checkmark beside their name.)
- Click “Start” to activate BotFather bot.In response, you receive a list of commands to manage bots.
- Choose or type the /newbot command and send it.
- Choose a name for your bot — your subscribers will see it in the conversation. And choose a username for your bot — the bot can be found by its username in searches. The username must be unique and end with the word “bot.”
- Copy the token value.
How to Create a New Bot for Telegram: https://sendpulse.com/knowledge-base/chatbot/telegram/create-telegram-chatbot
How to Get Your Telegram Chat ID: https://diyusthad.com/2022/03/how-to-get-your-telegram-chat-id.html
- In your Telegram account, search for “@myidbot” or open this link t.me/myidbot on your smartphone.
- Start a conversation with that bot and type /getid. You will get a reply back with your user ID.
- Note the user id as we’ll need it for our projects.
How to Create a Telegram Notifications for Conditions in Google Sheet
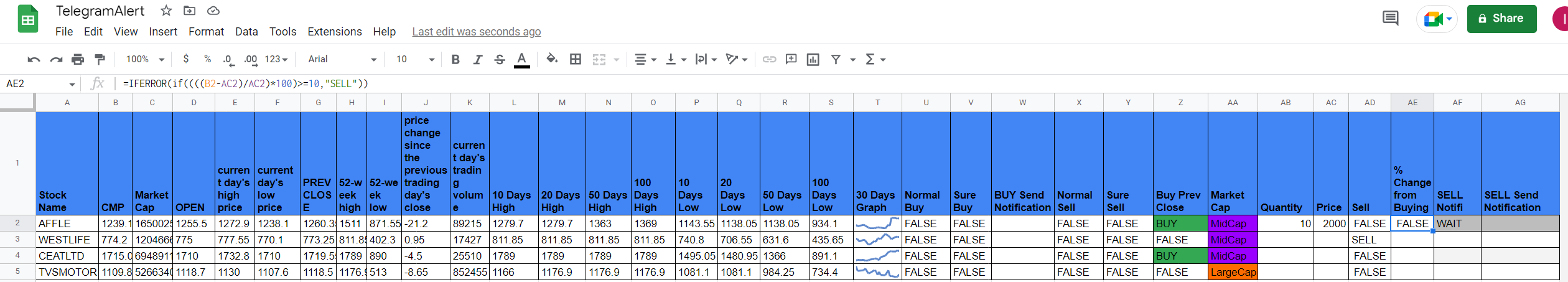
Let's take an example of the stock market in Google Sheets.
Create a Google Sheet in Google Drive and then click on "App Script".
Let's take a scenario, I want that when my bought stock prices increase by 10%, then I should receive a notification on my Telegram. For this, I have to enter the quantity and the buy price of the stock.
Go to "App Script", paste the below code and save it.
Paste This code:
var telegramtoken = "Your Telegram Bot Token";
var telegramURL = "https://api.telegram.org/bot"+telegramtoken;
function sendme(input,input1){
if(input != "WAIT"){
msg = "SELL StockName: "+input1+" Price: "+input
var url = telegramURL + "/sendMessage?chat_id=<Telegram ID of the message receiver>&text="+ msg;
var response = UrlFetchApp.fetch(url);
return "Message Sent";
}
}
Check all the formulas in the screenshots for a better understanding,
When the "SELL Notifi" column change from the "Wait" state to "SELL", a notification will send.

.png)





Comments
Post a Comment