Hello everyone, I am sharing a small change that I did in the detect-secrets tool which is my client's requirement. My client wants to use the “custom filter” in the Detect-Secrets but also wants, that no other option will be added while using it.
Example:
detect-secrets scan --filter custom_filter.py::is_invalid_secretThe reason to add the filter code in the tool code, so that anybody in the company, directly can use it without remembering any options and the path of the filter file like in the above example.
What is the filter in Detect-Secrets?
The filter is something that you don’t want to scan at the time of repo scan by detect-secrets. Like your organization use “AppID = dasdsfdsfsdfsf”, so for “Detect-secrets” this is secret but for your organization, it’s a normal value. So if you want fewer false-positive results then we use the filters.
How to add filter code in code and build the detect secret?
Step1: Clone the “Detect-Secrets” tool repo.
git clone https://github.com/Yelp/detect-secrets.git
Step2: Go to path “detect-secrets/detect_secrets/filters”
create a python file with any name. In my case, I am using “customfilter.py”
“customfilter.py”
import string
def is_likely_filter(secret, line):
line = line.lower()
if "AppID" in line:
return True
return FalseIn this code:
Detect-Secrets read line by line code, if detect-secrets find “AppID” in the line, it’s saying “return True” means it’s a filter “Ignore it” otherwise “return False”.
In the same way, you can declare your keywords here like “AppID”
Step3: Go to “detect-secrets/detect_secrets” and open “settings.py” file. Scroll down and add the path of your file like below:
'detect_secrets.filters.customfilter.is_likely_filter',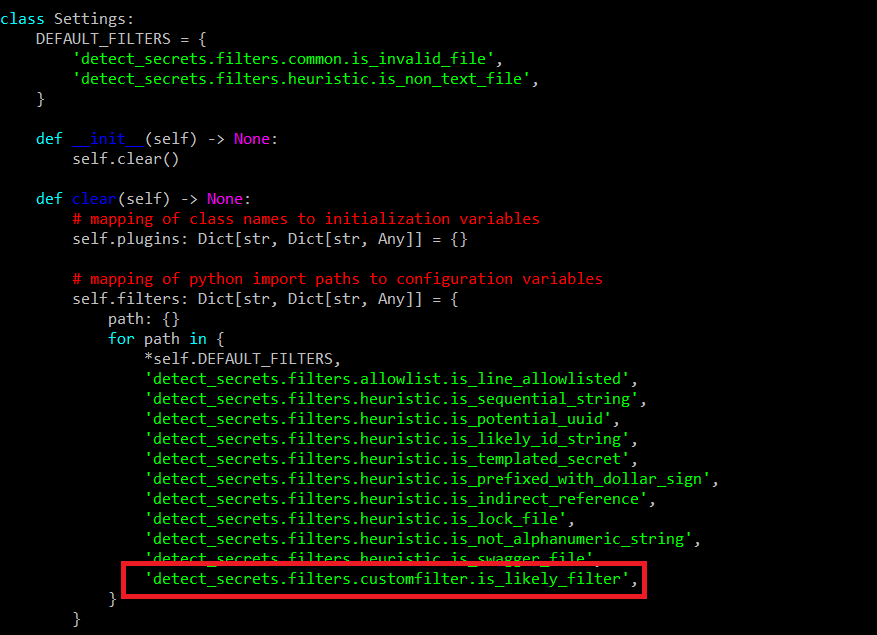
It’s a complete path of the “customfilter.py” and “is_likely_filter” is the method name in the file. Check the above code in step2.
Step4: Go to “detect-secrets” folder. Run the below command for building the code and installing the code.
python3 setup.py build
python3 setup.py install
Step5: Go to the path of the GitHub repo where you want to test your custom filter and run the below command.
detect-secrets scan > .secrets.baseline
detect-secrets scan --baseline .secrets.baselineNotes:
Whenever you add new code in the “customfilter.py”, you have to uninstall the detect-secrets and again build and install it.
For this, I have created a small bash script. Not completely check.
Copy in root directory “detect-secrets”
./addcustomfilter.sh AppID
This bash script automatically adds the AppID in the customfilet.py, uninstall the detect-secrets, again build and install it.
printf '\tif "'"$1"'" in line:\n\t\treturn True\n\treturn False\n' >> detect_secrets/filters/customfilter.py
pip3 uninstall detect-secrets
python3 setup.py build
python3 setup.py installHope this blog will help you if you are searching for the same scenario.
Comments
Post a Comment